PowerShell Gallery: Installing and Updating Modules Safely
The Module That Almost Shipped to Production A financial services client called us after a junior admin ran Install-Module on a domain controller during a maintenance window. The module pulled…
Working with YAML in PowerShell Using powershell-yaml
The Ticket That Started This Walkthrough The ticket said a scheduled DSC pull job was failing on three of seven nodes. Twenty minutes of log reading later, the pattern was…
Cybercrime Patterns Targeting Cloud Infrastructure in 2025
In March 2025, a mid-market SaaS company we monitor watched their AWS bill jump from $14,000 to $310,000 in eleven days. No new product launch. No traffic spike. An attacker…
Linux Process Management: ps, top, kill, and systemctl Audit
The 3 AM Page That Started This Checklist A logistics client paged us at 3 AM because their order API was returning 502s. The fix took ninety seconds once we…
Encryption Key Management Across AWS, Azure, and GCP
It is 3:14 AM and an alert fires from our SIEM. A developer at a fintech client just exported a customer master key reference from a CI pipeline log. The…
PowerShell Remoting Auth: Kerberos vs NTLM vs CredSSP
The 2 AM Call That Started This Post A managed customer paged us last quarter. Their nightly PowerShell job hit a remote file server, then tried to copy from a…
AWS Cost Explorer: Finding Waste and Right-Sizing EC2 Instances
The Invoice That Started a Three-Month Cleanup Project When one of our managed services clients forwarded their AWS invoice last quarter with the subject line “is this normal?”, I already…
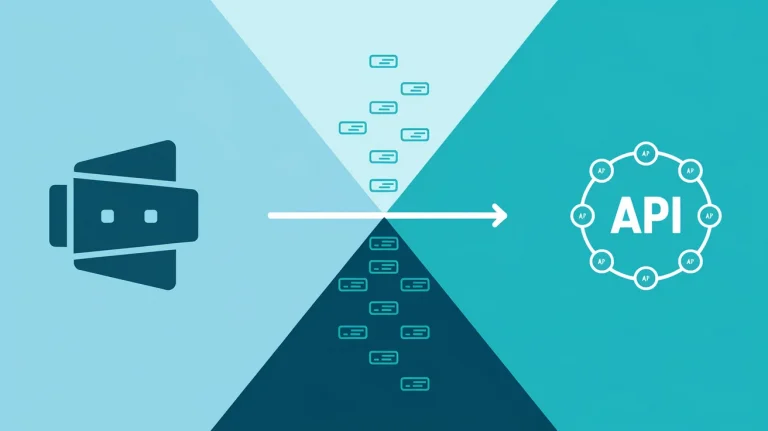
PowerShell REST API Calls with Invoke-RestMethod: A Practical Guide
Where this started While working on a monitoring integration for a logistics client, I got an idea for a small helper script that would pull ticket counts from their ITSM…
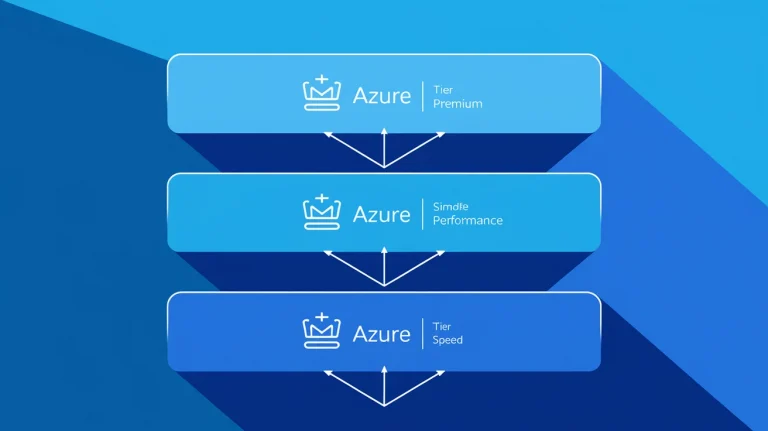
Azure CDN in 2026: Still Worth It, But Pick Your Tier
A retail client called us last spring after their Black Friday rehearsal ended with origin servers melting at 40% of projected traffic. They had a CDN switched on — Azure…
S3 Bucket Region Selection Strategy for Veeam Cloud Backups
A manufacturing client called us at 04:12 on a Saturday because us-east-1 was having one of its quarterly bad days. Their Veeam backups were green for eighteen months straight. They…